Hey there, fellow tech enthusiasts! In a world where our lives are increasingly online—from banking to chatting with friends—keeping our data safe is more crucial than ever. Enter RSA, one of the cornerstones of modern cryptography. Named after its inventors Ron Rivest, Adi Shamir, and Leonard Adleman, this algorithm has been safeguarding sensitive information since its debut in 1977.
But how does it actually work?!
In this blog post, I’ll break it down step by step, using simple analogies and a touch of math (don’t worry, I’ll keep it light). Whether you’re a crypto newbie or just curious about the “magic” behind secure websites, let’s dive in.
What is RSA and Why Does It Matter?
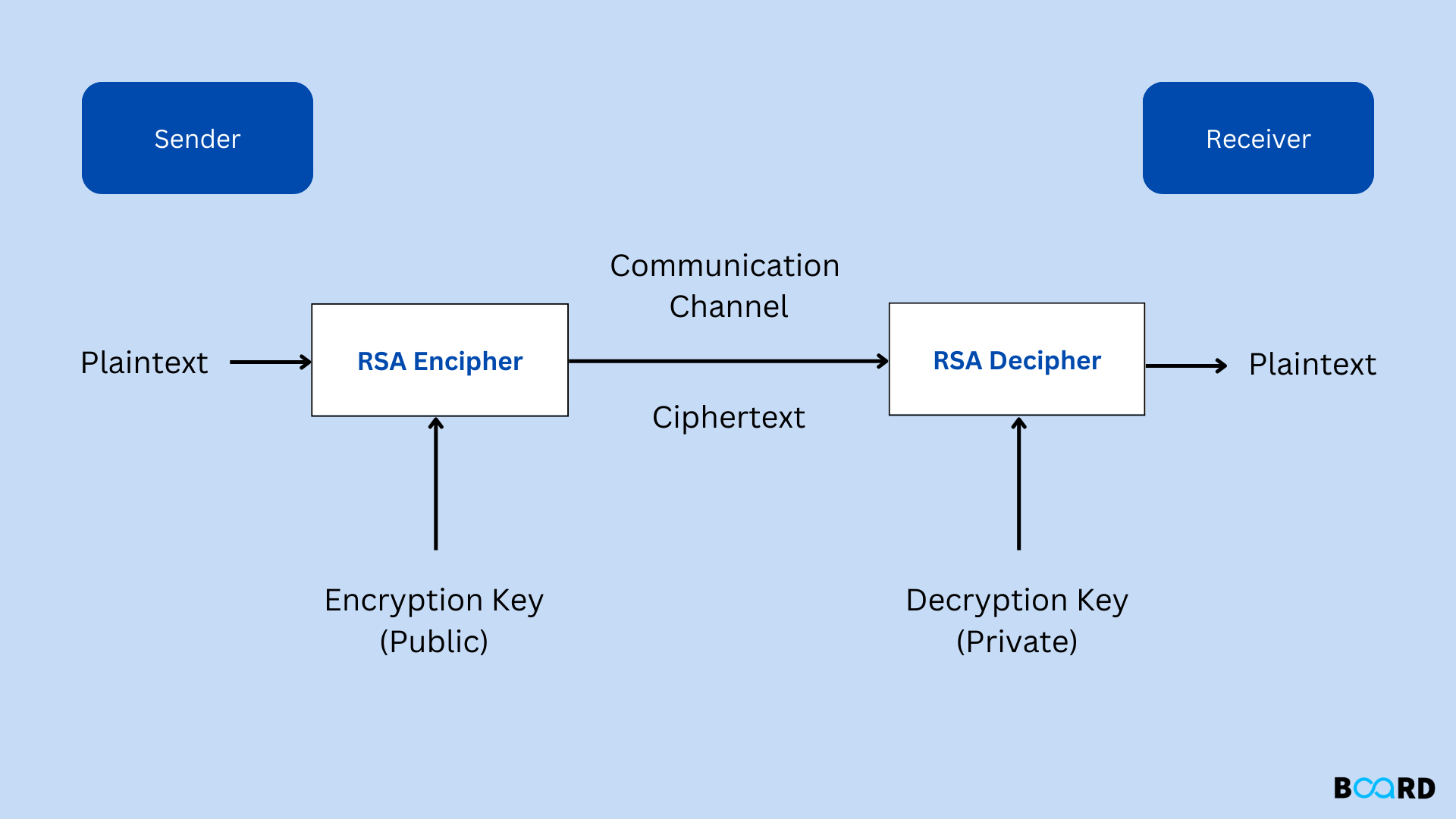
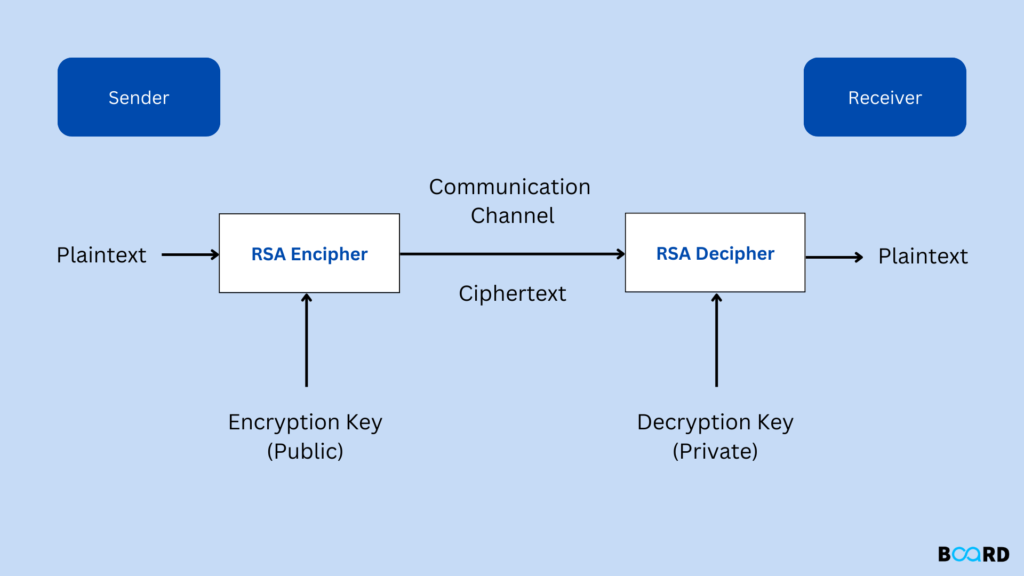
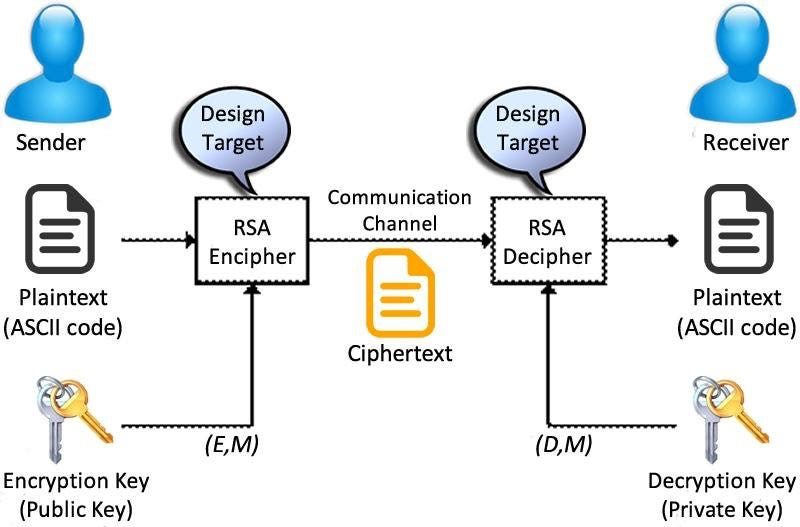
Imagine you’re sending a secret message in a crowded room. You don’t want just anyone to read it, right? Traditional symmetric encryption is like sharing a single key with your friend—efficient, but risky if that key gets intercepted. RSA flips the script with asymmetric encryption: it uses a pair of keys, one public (that anyone can see) and one private (that only you control). This allows secure communication without ever sharing the secret key upfront.
RSA is everywhere—from HTTPS connections on websites to digital signatures in emails. Its strength lies in the difficulty of factoring large prime numbers, a problem that’s easy to set up but insanely hard to reverse-engineer.
Think of it as a one-way lock: anyone can lock the door with the public key, but only the private key holder can unlock it.
The Math Magic: Primes and Moduli
At its heart, RSA is a beautiful blend of number theory. It starts with two large prime numbers, let’s call them p and q. These aren’t your everyday primes like 2 or 3; we’re talking massive ones, hundreds of digits long, chosen randomly and kept secret.
- Compute the Modulus (n): Multiply p and q to get n = p × q. This n becomes part of the public key. Factoring n back into p and q is the hard part—that’s what keeps hackers at bay.
- Euler’s Totient Function (φ(n)): Calculate φ(n) = (p-1) × (q-1). This counts how many numbers up to n are coprime (sharing no factors other than 1) with n. It’s a secret ingredient for key generation.
- Choose the Public Exponent (e): Pick a number e that’s coprime with φ(n) (gcd(e, φ(n)) = 1). Common choices are small primes like 3, 5, or 65537 for efficiency.
- Find the Private Exponent (d): Solve for d such that (d × e) mod φ(n) = 1. In other words, d is the modular inverse of e modulo φ(n). This is done using the Extended Euclidean Algorithm.
Now, the public key is the pair (e, n), and the private key is (d, n). Share the public key far and wide, but guard the private one like your life depends on it!
How Encryption Works
Sending a message? Convert your plaintext (say, “Hello”) into a number m (using ASCII or padding schemes). Then, encrypt it to ciphertext c with:
c = m^e mod n
That’s modular exponentiation—raising m to the power of e, then taking the remainder when divided by n. It’s computationally feasible even for big numbers thanks to efficient algorithms like binary exponentiation.
Decryption: Unlocking the Secret
The receiver uses the private key:m = c^d mod nVoilà! You get back the original m. Why does this work? It’s rooted in Euler’s theorem: since e and d are inverses modulo φ(n), m^{e×d} ≡ m mod n for m coprime to n. (In practice, RSA uses padding to handle edge cases.)
Why is RSA Secure? The Prime Factorization Puzzle
The security hinges on the fact that factoring n into p and q is computationally infeasible for large primes. With current tech, cracking a 2048-bit RSA key would take billions of years—even with supercomputers. However, quantum computers (via Shor’s algorithm) pose a future threat, which is why we’re shifting toward post-quantum crypto.That said, RSA isn’t invincible. Weak implementations (like small primes or predictable randomness) can be broken. Always use strong, random primes and proper padding (e.g., OAEP) to avoid attacks like Bleichenbacher’s.
Real-World Applications and Tips
RSA powers SSL/TLS for secure browsing, VPNs, and even blockchain tech for digital signatures. In cryptocurrencies, it’s used in wallets to sign transactions without revealing private keys.If you’re implementing RSA (say, in Python), libraries like PyCrypto or cryptography handle the heavy lifting. But remember: for production, use established libraries—don’t roll your own crypto!
Wrapping Up: The Enduring Legacy of RSA
RSA isn’t just an algorithm; it’s a testament to how pure math can solve real-world problems. As we venture deeper into the digital age, understanding tools like RSA empowers us to stay secure. Got questions or want to dive into elliptic curve crypto next? Drop a comment below—I’d love to hear from you! Stay safe online, folks. Until next time! 😀